Your Firewall Can’t Block Port 443
Your customers need it open. So do attackers. TarPit.pro identifies who's who, and blocks attackers from everything, including your live services.
# Your firewall rules:
port 22 OPEN ← attackers try SSH
port 80 OPEN ← attackers try HTTP
port 443 OPEN ← attackers try HTTPS
port * DROP ← everything else blocked
Attackers have full access to your
live services. Firewall can't help.
# Attacker scans your server:
→ :3306 MySQL FAKE BANNED
# Now blocked from ALL ports:
port 22 BLOCKED ← can't reach SSH
port 80 BLOCKED ← can't reach HTTP
port 443 BLOCKED ← can't reach HTTPS
Attacker can't see your server.
Customers connect normally.
Nobody with good intentions connects uninvited to a fake MySQL on port 3306. Anyone who does is not a customer. Ban them from everything, including the ports your customers need open.
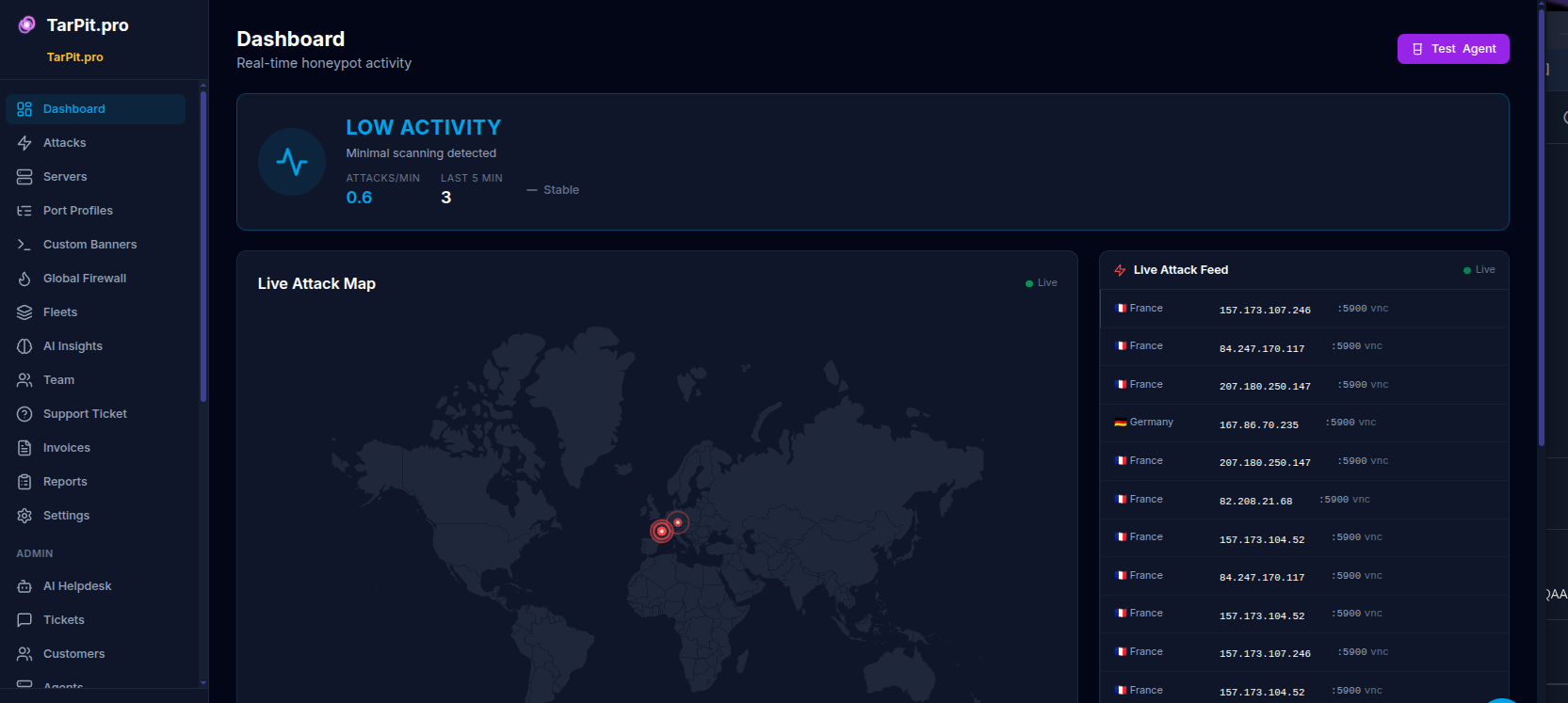
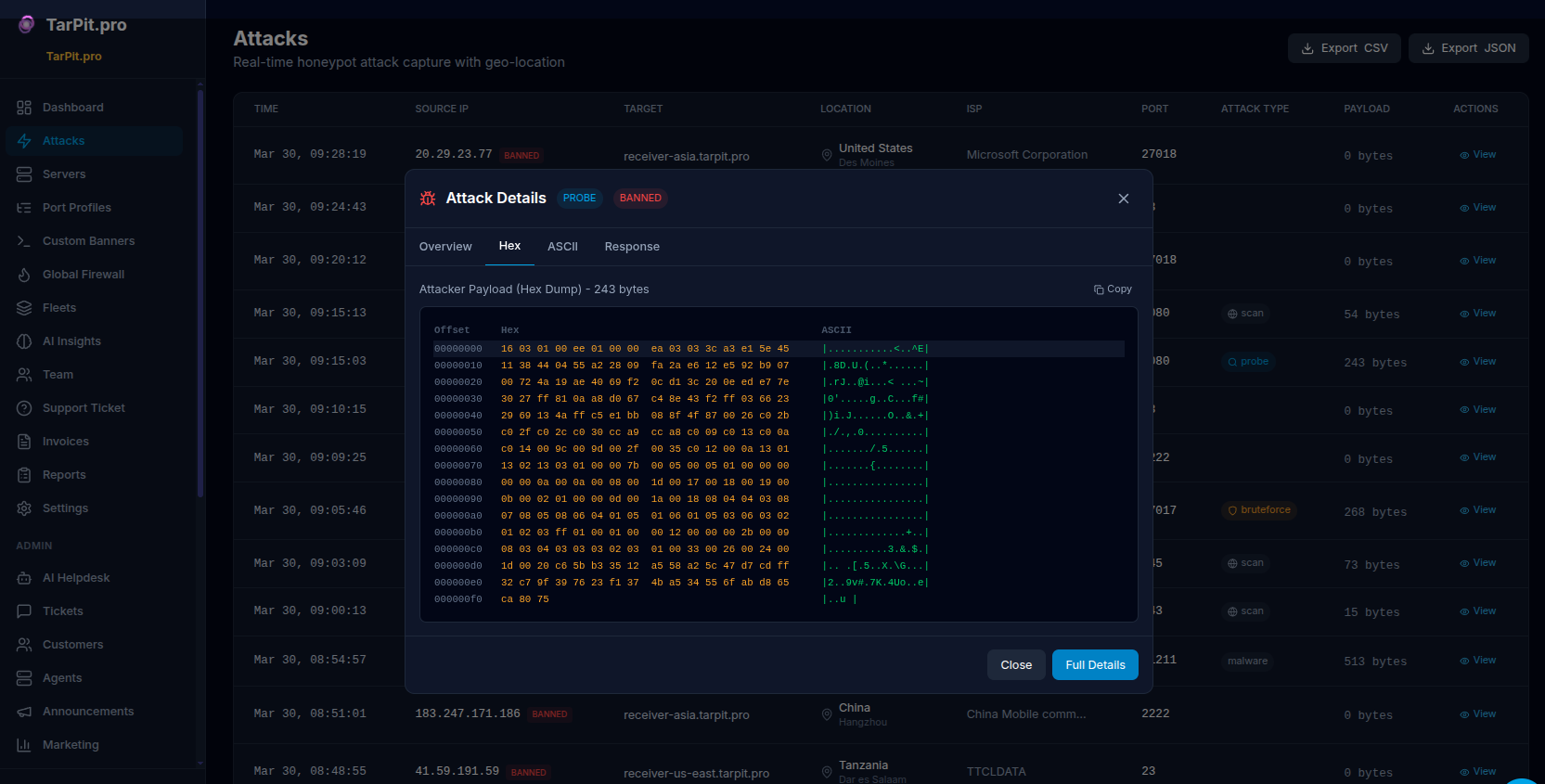
One Dashboard. Every Server. Every Attack.
Real-time attack map, detailed logs with payloads, and fleet-wide ban management. The screenshots your clients will love in monthly reports.
The Math Is Simple
SSH, MySQL, Redis, Telnet, RDP, VNC, SMB, all fake, all with realistic banners
Scanners probe sequentially. With 30 fake ports and 2-3 real ones, they almost always hit a trap first
No customer ever connects to a fake MySQL on port 3306. Every connection is malicious. Every ban is correct.
Your firewall protects closed ports. TarPit.pro protects the open ones, by making sure only customers can reach them.
Real Data from Real Honeypots
5 servers, 3 regions, 9 days. Every one of these IPs would have had full access to our live services.
Most Attacked Ports
The same IPs that hit these fake ports would have tried your real ones next.
Attack Types
53% is brute-force. Not sophisticated, just relentless. And it only takes one success.
Top Source Countries
US leads, attackers rent cheap cloud VPS instances there.
Up and Running in 60 Seconds
One command to install. One command to start. No Docker, no dependencies, no config files.
Install
Single binary. Linux, macOS, Windows. No Docker, no dependencies.
curl -sSL https://get.tarpit.pro | sh
Activate
Register free at tarpit.pro, grab your license key, activate.
tarpit-pro activate YOUR_KEY
Start
Fake ports go live. Attackers get caught and banned from ALL ports via iptables, including your real services.
sudo tarpit-pro start
Watch
Open the dashboard. See who's been trying to reach your servers. They can't anymore.
tarpit-pro status # 30 ports active, 47 IPs banned # Uptime: 3d 14h 22m
Not a Replacement. A Filter.
Your firewall, fail2ban, WAF, they all still do their job. TarPit.pro makes them better by filtering out attackers before they reach any of it.
Without TarPit.pro
Attacker gets 5 free shots at your real SSH before anything happens.
With TarPit.pro
Attacker never reaches SSH, HTTP, or anything real. Zero attempts on live services.
Built For Teams That Manage Servers
Whether it's 2 servers or 200, every one of them has open ports that attackers can reach right now.
MSPs
Deploy across all client servers in minutes. Fleet bans propagate instantly. One attacker caught on one server can't reach any of your clients.
Learn moreWeb Agencies
Attackers scanning port 3306 on your WordPress servers get banned before they ever find wp-login on port 443. Your clients' sites become invisible to scanners.
Learn moreE-commerce
Your checkout runs on 443. So do carding bots. TarPit.pro catches them on fake ports first and blocks them from your entire store.
Learn moreSaaS & Startups
Your API is on 443. Your database is firewalled but your app server isn't. TarPit.pro filters out attackers before they probe for vulnerabilities.
Learn moreHow It Pays for Itself
Deploy in 60 Seconds
One install command per server. No config files, no Docker, no firewall rules to write. Runs as a systemd service.
Show Clients the Data
“Your server blocked 847 attackers from all services this month.” That's a line item that justifies itself.
Fleet-Wide Protection
One server catches an attacker, all servers in the fleet ban them. One dashboard for every client, every server.
Your Live Services Are Open Right Now
Every attacker scanning the internet can reach your port 22, 80, and 443. Start filtering them out in 60 seconds. Free for 2 servers, no credit card.
Paid plans from $10/server/month for fleet management, extended storage, and CVE detection. See pricing
Get Started Free